Many security teams start the same way in the morning. Slack threads. News alerts. Researcher blogs. Vendor advisories. A zero-day trending on social media. A CISA bulletin that just dropped.
Public intelligence is often the earliest signal we get about emerging risk. And yet, in most organizations, it rarely becomes operational in a consistent way.
Someone reads it. Someone forwards it. Someone asks, “Does this apply to us?” Then the real work begins. Manual validation. Internal cross-checking. A few strong opinions. Maybe a meeting. Eventually, a decision.
The problem isn’t access to information. The problem is systematically turning public knowledge into defensible action.
Today, we’re introducing Public Knowledge Agents, now generally available in the Brickleyer agentic cybersecurity platform. This capability converts curated public sources into structured intelligence that can be reasoned over directly inside your security workflows. It closes the gap between awareness and execution.
The Friction Security Leaders Know
If you’ve ever been in a risk review and been asked why something is prioritized, you know the tension.
A vulnerability may be all over the news, but your environment isn’t exposed. A vulnerability may look critical, but exploitation requires conditions you don’t have. Leadership may react to headlines while your team is trying to stay grounded in actual exposure.
Public intelligence creates urgency. Internal context determines relevance. The hard part is bringing those together consistently and at scale.
Historically, that bridge depended on individuals and tribal knowledge. Who read the info? Who follows the right researchers? Who noticed the nuance buried halfway through a vendor write-up?
Public Knowledge Agents formalize how external intelligence is collected, evaluated, and applied to make faster, smarter decisions.
How Public Knowledge Agents Work
Public Knowledge Agents operate as a first-class component inside Brickleyer’s multi-agent architecture.
Organizations explicitly define which public sources they trust and want included. These can include:
- Security researchers and collectives
- Vendor research blogs
- Government alerts and regulatory guidance
- Compliance bodies and standards organizations
- Incident postmortems and playbooks
- Trusted security media
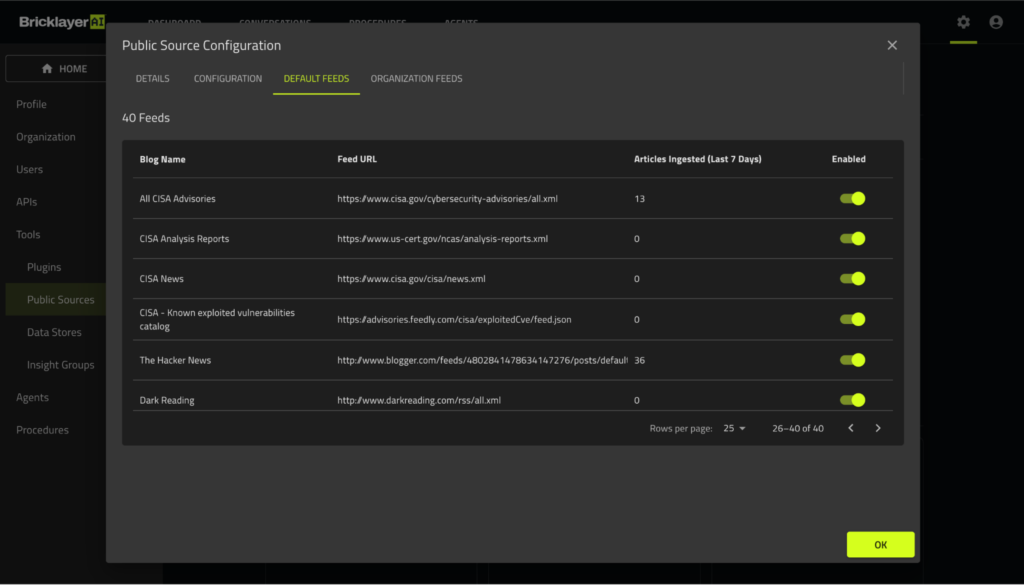
Brickleyer AI provides a preconfigured set of feeds, including public knowledge sources such as CISA, Hacker News, and Dark Reading. Each can be enabled or disabled individually. Teams can also customize by adding additional URL-based feeds through a simple interface.
These sources are ingested hourly and transformed into structured external intelligence. No manual polling. No bookmarking. No copy-pasting links into tickets.
Once ingested, this intelligence lives alongside internal telemetry, data sources, policies, procedures, and risk posture inside the platform.
That is where the real value emerges.
Integrated into Workflows, Not Sitting on the Side
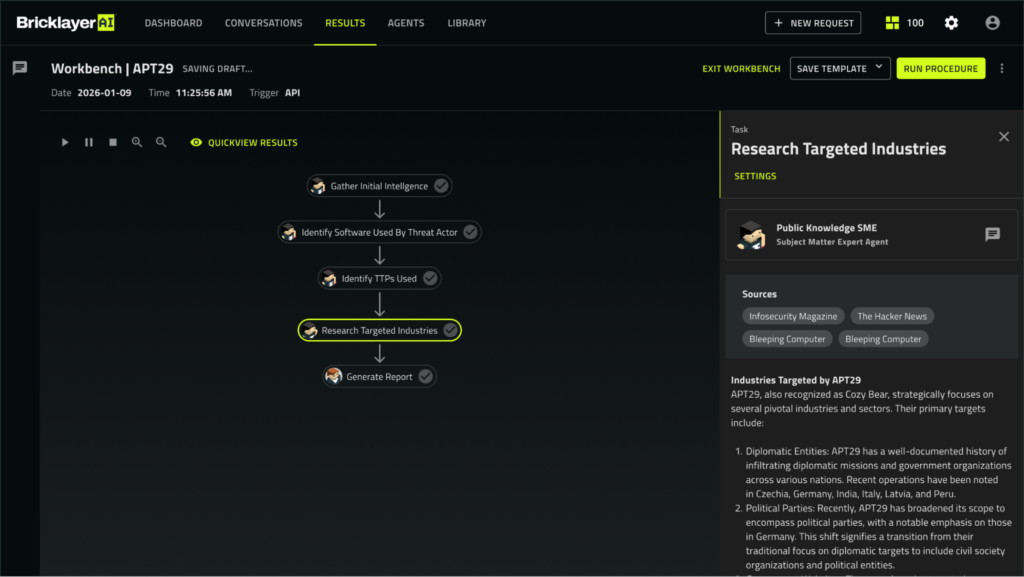
Public Knowledge Agents are invoked as part of governed workflows within the Brickleyer AI system. They operate with persistent context about the environment, coordinate seamlessly with other agents and humans, and remain under control with every decision transparent and auditable.
Public knowledge retrieval can occur:
- As part of scheduled processes
- When triggered by a user request
- During an investigation
- As a step inside a defined procedure
When a role-based agent needs external context, it queries the Public Knowledge Agent at that moment. The retrieved intelligence is evaluated against organizational data such as asset criticality, exposure, deployed technologies, existing controls, and business priorities.
If the initial context is insufficient, the agent can retrieve additional authoritative sources to close gaps before producing a recommendation.
Every conclusion is traceable to curated public sources, which reduces noise and misinformation risk and ensures consistency across teams.
It provides the operational intelligence to determine “here’s what this means for us, given our environment.”
How Security Teams Put This Into Action
Executive and Board Reporting
Agents can generate briefings that combine internal posture with relevant external developments. When explaining why a risk is prioritized or deprioritized, teams can reference authoritative public sources alongside internal context. That changes the nature of leadership conversations.
Example: A Brickleyer AI Threat Intelligence Analyst agent produces an executive report on APT29 based on the various sources of data collected and analyzed by Public Knowledge Agents.
Evaluating Emerging Threats
When a new exploit starts trending, agents determine whether affected technologies are actually deployed, where exposed assets sit, and what compensating controls exist. The result is a defensible assessment of organizational relevance, not a reaction to headlines.
Incident Response
During an active investigation, agents can incorporate vendor mitigation guidance, community playbooks, and lessons learned from similar incidents. Recommendations are aligned with the tools and processes your team actually uses.
Vulnerability Management
Public research often includes nuances that severity scores miss. Exploit maturity, reliability, configuration-specific exposure, evidence of real-world targeting. When evaluated alongside internal asset data, prioritization becomes more rational and easier to justify.
Compliance and Regulatory Alignment
Regulators and standards bodies increasingly publish guidance through blogs, alerts, and public interpretations before formal updates are codified. Public Knowledge Agents can retrieve this guidance and evaluate it against your existing controls and policies.
Where Public Intelligence Becomes Operational
Security programs should not depend on who happened to read which post this week.
Public Knowledge Agents move public intelligence from informal reading to structured reasoning inside governed agentic AI workflows. Harnessing external knowledge becomes part of your operating model and decision making.
As the threat landscape evolves, your decision-making evolves with it. Transparently. In context.
Public Knowledge Agents are now generally available in Brickleyer AI.
If you’ve ever wished public intelligence could consistently integrate into your operations instead of living in disparate threads and minds, book a demo to see how this works in practice.